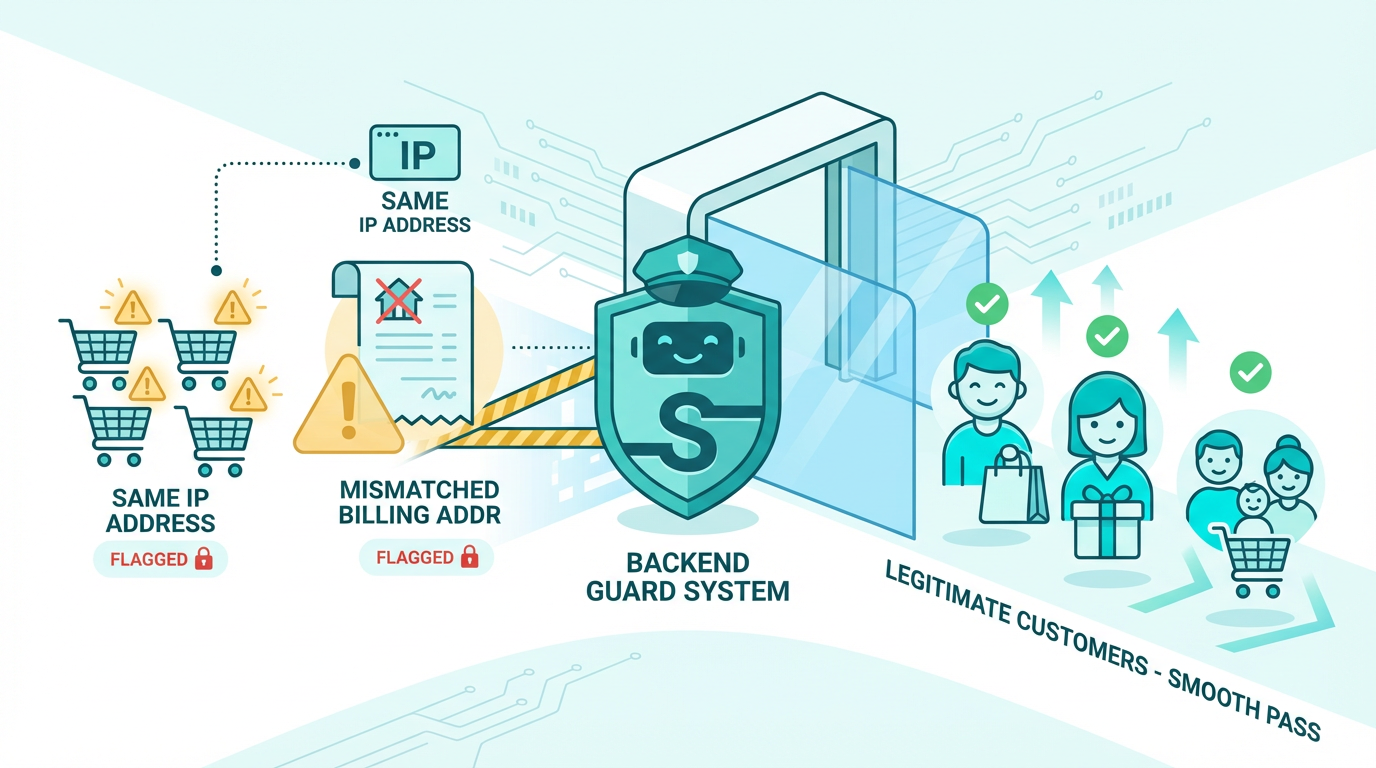
Someone places 20 orders in 5 minutes using different credit cards but the same IP address. Another customer enters a New York billing address but ships to Romania. These patterns scream fraud, but you won’t catch them manually. A backend runs fraud detection rules automatically. It checks how many orders come from one IP, compares billing and shipping addresses, flags unusually large purchases, and blocks suspicious cards before charging them. Stripe and PayPal offer fraud tools, but your backend decides which rules to enforce.
Why fraud hits small businesses harder than anyone else
Large enterprises have dedicated fraud teams, sophisticated machine learning models, and insurance policies that cover losses. When a fraudster steals $10,000 from Amazon, it barely registers. When the same fraudster hits your $200,000 revenue startup, it’s a catastrophic month.
Small businesses absorb fraud losses directly because they lack the volume to spread risk across millions of transactions. A single chargeback costs you the product value, the shipping cost, a $15-25 chargeback fee from your payment processor, and potentially your merchant account if your chargeback rate exceeds 1%. Lose your merchant account and you can’t accept credit cards at all, which effectively ends your business.
Fraudsters know this and actively target small businesses precisely because their defenses are weaker. They test stolen credit cards on small sites before using them for large purchases elsewhere. They place orders knowing small businesses rarely have automated fraud detection catching patterns that humans can’t monitor manually.
Your backend levels this playing field by running the same pattern detection that enterprise fraud teams use, automatically and continuously, without requiring a dedicated security hire.
The three fraud patterns that cost businesses the most
Understanding which fraud types are most common helps you configure your backend’s detection rules effectively. Most payment fraud falls into three categories, each with distinct patterns your backend can identify.
Card testing happens when fraudsters use your checkout to verify whether stolen credit card numbers work. They place small orders, often under $5, using dozens of different cards in rapid succession. If the charge succeeds, the card is valid and they’ll use it for larger purchases elsewhere. Your backend detects card testing by flagging accounts that attempt multiple failed payments within a short window, then blocking further attempts from that IP address or device fingerprint.
Account takeover fraud occurs when someone gains access to a legitimate customer’s account and changes the shipping address before placing orders. Your backend detects this by flagging orders where the shipping address changed within 24 hours of the purchase, triggering additional verification before processing the payment.
Friendly fraud, the most frustrating category, happens when legitimate customers complete genuine purchases then dispute the charge with their bank claiming they never received the item or never authorized the transaction. Your backend protects against friendly fraud by storing detailed purchase records, delivery confirmations, and usage logs that you submit as evidence when disputing chargebacks.
Building detection rules that catch fraud without blocking real customers
The biggest challenge in fraud prevention isn’t catching fraudsters, it’s catching them without accidentally blocking legitimate customers. Overly aggressive rules create false positives where genuine customers get blocked and take their business elsewhere.
A customer in New York buys a gift and ships it to a friend in Romania. Your fraud rule flags international shipping addresses and blocks the order. The customer is legitimate, confused, and frustrated. They contact support, you manually approve the order an hour later, but the experience damaged their trust.
Building these detection rules correctly requires understanding how your entire backend processes transactions from the moment a customer clicks buy now, which is covered in detail in how a backend handles your digital cashier.
Effective fraud rules use multiple signals together rather than single triggers. Instead of blocking all orders shipping internationally, your backend flags orders that ship internationally AND use a card registered in a different country AND were placed by an account created within the last hour AND exceed $200 in value. All four conditions together indicate fraud far more reliably than any single condition alone.
This multi-signal approach reduces false positives dramatically. Legitimate international gift purchases usually fail only one or two of these conditions. Actual fraud attempts typically trigger three or four simultaneously.
Velocity checks that catch fraud in real time
Velocity checks measure how quickly certain actions happen. Fraudsters work fast because stolen card details have short windows of validity before banks detect them. A legitimate customer browses your store for ten minutes, compares products, reads reviews, and places one order. A fraudster places twenty orders in two minutes.
Your backend implements velocity checks by counting specific events within time windows. More than three failed payment attempts from the same IP address within ten minutes triggers a temporary block. More than five orders from the same account within one hour flags the account for review. More than $500 in purchases from a new account within 24 hours requires additional verification.
These thresholds need calibration based on your specific business. A flash sale might legitimately generate high order volumes from individual customers. A B2B platform might have procurement officers placing dozens of orders in quick succession. Your backend lets you adjust velocity thresholds based on context, applying stricter rules to new accounts and relaxing them for established customers with clean purchase histories.
Supabase edge functions run velocity checks in milliseconds during checkout. Before your payment function calls Stripe, it queries the database for recent activity from the current IP and account, calculates whether any velocity thresholds are exceeded, and either proceeds with payment or returns a fraud flag. The entire check adds less than 100 milliseconds to checkout time, invisible to legitimate customers.
Address verification that stops stolen cards immediately
When a fraudster uses a stolen credit card, they usually don’t know the cardholder’s billing address. Banks use Address Verification Service, the system that matches billing addresses to card records, to catch these cases before charges complete.
Your backend passes the customer’s entered billing address to Stripe, which forwards it to the card’s issuing bank for verification. The bank returns a code indicating whether the street address matches, the zip code matches, both match, or neither matches. Your backend uses this code to decide whether to proceed with the payment.
A full address match proceeds normally. A zip code match with street mismatch might proceed with a fraud flag added to the order for manual review. No match on either field declines the payment automatically and asks the customer to verify their billing address.
Legitimate customers whose cards decline due to address mismatch are usually entering their address incorrectly, transposed numbers, old address on file with the bank, or corporate cards with registered billing addresses different from their workplace. Your backend shows a helpful error message asking them to check their billing address rather than a generic decline message, reducing legitimate customer frustration while still blocking fraudulent cards.
Device fingerprinting that identifies fraudsters across accounts
A fraudster whose IP address gets blocked simply creates a new account and tries again. IP blocking alone doesn’t stop determined bad actors. Device fingerprinting goes deeper by identifying the specific device being used, regardless of account or IP address.
Your backend collects technical details about the customer’s browser and device during checkout: screen resolution, installed fonts, browser plugins, operating system version, and dozens of other signals that together create a unique fingerprint. This fingerprint stays consistent even when the fraudster switches IP addresses or creates new accounts.
When a device fingerprint associated with previous fraud attempts appears again, your backend flags the session immediately. The fraudster sees the same checkout experience but their order gets flagged for review before processing. You investigate, confirm fraud, and block the order without the fraudster knowing their new account is already compromised.
This technique works because legitimate customers don’t think about device fingerprints. Only bad actors deliberately modify their device signatures, and doing so perfectly is technically difficult. The vast majority of returning fraudsters use the same device they used before.
Chargeback management that protects your merchant account
A chargeback happens when a customer disputes a charge with their bank instead of contacting you directly. The bank reverses the payment, charges you a fee, and gives you a short window to dispute the reversal with evidence.
Your backend automatically compiles evidence packages when chargebacks occur. It pulls the original order details, the IP address and device fingerprint from checkout, the delivery confirmation, any customer support interactions, and usage logs showing the customer accessed the product after purchase. This evidence package goes to Stripe, which submits it to the bank on your behalf.
Winning chargeback disputes requires documentation that most small businesses don’t maintain consistently. Your backend maintains it automatically for every transaction, making dispute resolution a matter of generating a report rather than hunting through emails and receipts.
More importantly, your backend tracks your chargeback rate continuously. Payment processors terminate merchant accounts when chargeback rates exceed 1% of monthly transactions. If your rate approaches this threshold, your backend alerts you so you can tighten fraud rules before losing your ability to accept credit cards.
Why prevention costs less than recovery every time
A fraud prevention system costs $0-50 monthly depending on the tools you integrate. Stripe Radar, the fraud detection built into Stripe, is free for standard accounts. TaxJar integration adds $19 monthly. Custom backend rules cost only the Supabase compute time to run them, typically pennies per month.
Compare this to the cost of fraud losses. The average chargeback costs $190 when you factor in the product value, shipping, chargeback fees, and time spent on disputes. A business processing 500 orders monthly with a 2% fraud rate loses $1,900 monthly to chargebacks alone. Over a year, that’s $22,800 in preventable losses.
Fraud prevention also protects something harder to quantify: your reputation with payment processors. A history of high chargebacks makes processors view your business as high-risk, leading to higher processing fees, payment holds, and potential account termination. Clean fraud metrics keep your processing costs low and your merchant account secure.
Once fraud prevention runs automatically, the final piece of the customer experience puzzle involves sending confirmation emails and receipts the moment legitimate orders complete. Automating order confirmations and thank you emails turns every successful transaction into a trust-building moment that keeps customers coming back.
Did you find this helpful?
Your feedback helps us curate better content for the community.